In our previous article, we explored how to integrate security into each phase of the software development lifecycle (SDLC) for general applications. Now, we will focus this knowledge on the world of embedded applications. In systems where hardware and software intersect, ensuring security is even more challenging and crucial. This article discusses how to adapt secure development practices to the context of embedded systems, offering insights, tips, and best practices to protect the devices that are part of our daily lives.
Why Focus on Security for Embedded Applications?
Embedded systems are present in various fields, such as automobiles, IoT devices, industrial equipment, and smart appliances. Unlike traditional software, these systems face unique challenges:
- Limited Resources: Processors, memory, and power are often constrained, limiting the implementation of complex security solutions.
- Hardware Integration: Direct interaction with physical components increases the attack surface, requiring specific measures to protect both software and hardware.
- Difficult Updates: Many embedded devices have long life cycles, and firmware updates can be complex or even unfeasible, making vulnerability prevention essential.
- Critical Environment: In industries such as automotive and industrial, security failures can have severe consequences, affecting user safety and system integrity.
These particularities highlight the importance of an SDLC adapted for embedded applications, where each phase must be carefully planned and executed with a security focus.
Challenges of Secure Development in Embedded Systems
Before diving into SDLC adaptation, it is crucial to understand the primary security challenges in embedded systems:
- Processing and Memory Limitations: Implementing encryption and other security measures may require resources that the device lacks.
- Diversity of Architectures: The variety of microcontrollers and embedded operating systems requires customized solutions and, often, the development of tailored code.
- Connectivity and Network Exposure: Connected devices can be targets for remote attacks, necessitating robust authentication mechanisms and encrypted communications.
- Hardware Integration: Hardware security, such as using trusted platform modules (TPM) or secure boot, must be integrated into software development.
Recognizing these challenges is the first step in building a secure development strategy that minimizes risks and ensures the robustness of embedded systems.
Adapting SDLC for Embedded Applications
As with traditional applications, the SDLC for embedded systems can be divided into phases. However, each stage requires special attention due to the constraints and requirements of embedded devices.
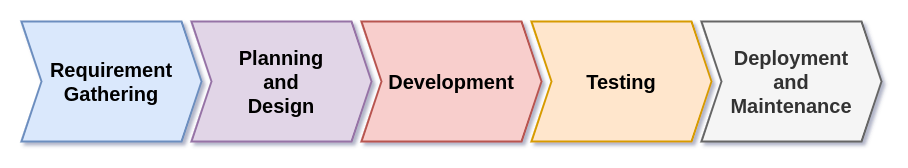
1. Requirements Gathering and Planning
At this stage, it is essential to define the scope and system requirements, considering both functionalities and hardware-imposed constraints.
- Definition of Functional and Non-Functional Requirements:
- Functional: What the device must do (e.g., monitoring, process control, communication).
- Non-Functional: Performance, power consumption, response time, and, most importantly, security requirements.
- Risk Management:
- Identify potential threats specific to embedded systems, such as attacks on physical interfaces, communication interception, and firmware vulnerabilities.
- Compliance Requirements and Certifications:
- Consider standards and certifications specific to embedded devices, such as NIST guidelines, FIPS, or security standards for the automotive and IoT industries.
- Planning for Updates and Maintenance:
- Establish strategies for firmware updates, considering the difficulties of physical access and the need to minimize service interruptions.
2. Design and Architecture
In embedded systems design, the integration between hardware and software requires detailed planning to ensure security measures are effective and compatible with device limitations.
- Threat Modeling:
- Conduct threat modeling focused on unique embedded system risks, such as physical attacks (e.g., firmware extraction), exploitation of communication interfaces, and sensor manipulation.
- Attack Surface Evaluation:
- Identify vulnerabilities in both software and hardware. Consider security for interfaces like USB, Bluetooth, Wi-Fi, and other connectivity methods.
- Implementation of Hardware Security Measures:
- Use technologies such as secure boot, TPM modules (Trusted Platform Module), and memory encryption to ensure device integrity from startup.
- Defense-in-Depth Architecture:
- Combine security measures at different levels—from hardware to software—to create complementary protection layers.
3. Secure Development and Implementation
During development, secure coding practices must be adapted to the reality of embedded systems.
- Secure Coding Practices for Firmware:
- Follow specific guidelines for programming in resource-limited environments, avoiding common vulnerabilities such as buffer overflows and code injection.
- Dependency and Library Management:
- Ensure the security of the libraries and drivers used. In embedded systems, the compatibility and efficiency of these dependencies are critical.
- Resource Optimization:
- Implement security solutions that are efficient in processing and memory usage without compromising device performance.
- Continuous Integration and Unit Testing:
- Adopt DevSecOps practices adapted for embedded systems, ensuring that each modification is tested for security and performance flaws.
4. Testing, Verification, and Validation
Testing embedded devices requires methodologies that cover both software and hardware.
- Static and Dynamic Firmware Testing:
- Use tools for static code analysis to identify potential vulnerabilities and dynamic testing to simulate real attacks in the device environment.
- Specialized Code Reviews:
- Conduct code reviews focused on embedded development specifics, considering security, performance, and efficient resource usage.
- Hardware-Software Integration Testing:
- Ensure that communication between hardware and software components is secure and functions as intended.
- Validation of Communication Protocols:
- Ensure that implemented communication protocols, such as MQTT for IoT or CAN for automotive applications, are properly encrypted and authenticated to prevent interception and manipulation.
5. Deployment, Operation, and Maintenance
The deployment and maintenance phase in embedded systems require specific precautions due to the inherent challenges of updates and remote monitoring.
- Firmware Update Management:
- Develop secure over-the-air (OTA) update strategies, ensuring that only authenticated firmware is installed and that the device can recover from update failures.
- Continuous Monitoring and Remote Diagnostics:
- Implement monitoring systems that can detect abnormal behaviors and potential intrusions, enabling quick and effective responses.
- Incident Response Plans:
- Establish clear procedures for responding to security incidents, minimizing impacts, and ensuring device operational continuity.
- Device Lifecycle Management:
- Consider the complete lifecycle of the device, from production to disposal, implementing measures to protect data even in the final phases.
Frameworks and Tools for Embedded Systems Security
Adopting specialized frameworks and tools is essential to enhancing security in embedded applications. Some recommendations include:
- OWASP IoT Top 10:
- A list of the top vulnerabilities found in connected devices, serving as a guide for securing IoT and embedded systems.
- FIPS (Federal Information Processing Standards):
- Standards that establish security requirements for encryption and security modules in embedded devices.
- Common Criteria:
- An international standard providing a basis for evaluating the security of IT products, including embedded systems.
- Firmware Analysis Tools:
- Solutions that allow firmware code inspection and analysis to identify flaws and vulnerabilities before deployment.
Conclusion
Security in embedded applications requires an integrated approach adapted to the particularities of systems that combine hardware and software. By applying an SDLC specific to embedded systems, it is possible to:
- Minimize risks and vulnerabilities from requirements gathering to device maintenance.
- Ensure that resource constraints and hardware specifics are considered at every development stage.
- Adopt robust security measures that protect both software and hardware, promoting device reliability and resilience.
Investing in a secure development lifecycle for embedded applications is not just a best practice—it is a necessity to protect sensitive data, ensure service continuity, and, above all, guarantee user safety in an increasingly connected world.
If you want to continue deepening your knowledge of embedded systems security, stay tuned for upcoming articles. Also, explore other content on our blog to discover essential tips, frameworks, and practices to make your projects robust and secure.